
OpenClaw Skills Ecosystem and Practical Production Picks
The skills worth keeping, and the ones to skip
OpenClaw has two extension stories, and they are easy to mix up.
Plugins extend the runtime. Skills extend the agent’s behavior.

The skills worth keeping, and the ones to skip
OpenClaw has two extension stories, and they are easy to mix up.
Plugins extend the runtime. Skills extend the agent’s behavior.

How real OpenClaw systems are actually structured
OpenClaw looks simple in demos. In production, it becomes a system.

Hermes Agent install and quickstart for devs
Hermes Agent is a self-hosted, model-agnostic AI assistant that runs on a local machine or low-cost VPS, works through terminal and messaging interfaces, and improves over time by turning repeated tasks into reusable skills.

Remote Ollama access without public ports
Ollama is at its happiest when it is treated like a local daemon: the CLI and your apps talk to a loopback HTTP API, and the rest of the network never finds out it exists.

HTTPS Ollama without breaking streaming responses.
Running Ollama behind a reverse proxy is the simplest way to get HTTPS, optional access control, and predictable streaming behaviour.

Control data and models with self-hosted LLMs
Self-hosting LLMs keeps data, models, and inference under your control-a practical path to AI sovereignty for teams, enterprises, nations.

January 2026 trending Rust repos
The Rust ecosystem is exploding with innovative projects, particularly in AI coding tools and terminal applications. This overview analyzes the top trending Rust repositories on GitHub this month.

January 2026 trending Go repos
The Go ecosystem continues to thrive with innovative projects spanning AI tooling, self-hosted applications, and developer infrastructure. This overview analyzes the top trending Go repositories on GitHub this month.

Melbourne's essential 2026 tech calendar
Melbourne’s tech community continues to thrive in 2026 with an impressive lineup of conferences, meetups, and workshops spanning software development, cloud computing, AI, cybersecurity, and emerging technologies.

Protect your privacy with advanced anti-fingerprinting
In the modern web, your digital identity can be tracked without cookies or explicit consent through sophisticated ditital fingerprinting techniques.

Privacy-preserving systems with zero-knowledge proofs
Zero-knowledge architecture represents a paradigm shift in how we design privacy-preserving systems.

Complete security guide - data at rest, in transit, at runtime
When data is the a valuable asset, securing it has never been more critical. From the moment information is created to the point it’s discarded, its journey is fraught with risks - whether stored, transferred, or actively used.

Deploy production-ready service mesh - Istio vs Linkerd
Discover how to implement and optimize service mesh architectures using Istio and Linkerd. This guide covers deployment strategies, performance comparisons, security configurations, and best practices for production environments.
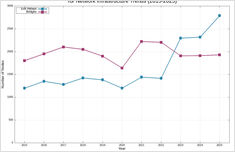
Analyzing Tor network growth and challenges over a decade
The Tor network has experienced significant fluctuations in its infrastructure over the past decade, with exit relays and bridges showing distinct patterns of growth, decline, and recovery.