Building a Dual-Mode AWS Lambda with Python and Terraform
Step-by-step example
Here we have a Python Lambda example of SQS Message Processor + REST API with API Key Protection + Terraform script to deploy it for serverless execution.
AWS Lambda lets you write lightweight serverless functions that can react to almost any event — from SQS messages to HTTP requests. In this guide, we’ll build a single Python Lambda that works in two modes:
- SQS mode: When triggered by an SQS message like
{ "par": 10 }, it publishes{ "res": 11 }to another queue. - HTTP mode: When called via API Gateway at
GET /lam?par=10, it returns{ "res": 11 }to the client.
We’ll also protect the HTTP endpoint using a simple hardcoded API key — "testkey".
The entire setup will be deployed using Terraform.
Architecture Overview
Let’s visualize what we’re building:
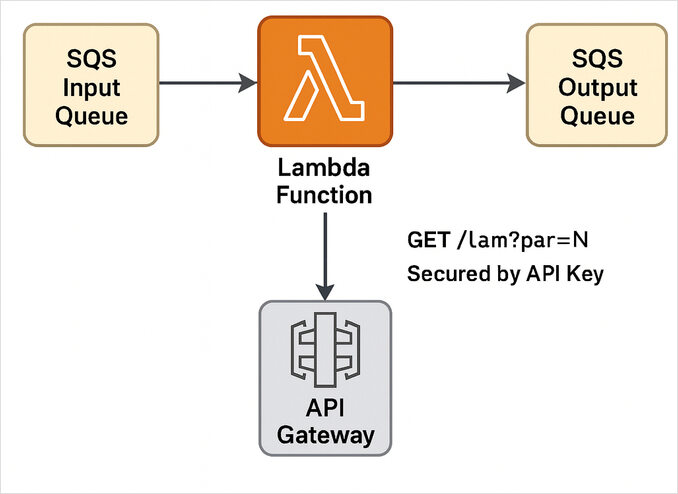
The same Lambda reacts to both:
- SQS events, via an event source mapping, and
- API Gateway requests, via a RESTful HTTP integration.
Step 1: Create the Lambda in Python
Let’s create a very simple handler in Python that can distinguish between an SQS event and an HTTP API call.
File: lambda_function.py
import json
import os
import boto3
sqs = boto3.client("sqs")
OUTPUT_QUEUE_URL = os.environ.get("OUTPUT_QUEUE_URL")
API_KEY = os.environ.get("API_KEY", "testkey") # hardcoded default
def lambda_handler(event, context):
# Detect event type
if "Records" in event: # SQS event
return handle_sqs(event["Records"])
else: # HTTP event
return handle_http(event)
def handle_sqs(records):
for record in records:
body = json.loads(record["body"])
par = int(body["par"])
res = par + 1
message = json.dumps({"res": res})
sqs.send_message(QueueUrl=OUTPUT_QUEUE_URL, MessageBody=message)
return {"status": "processed", "count": len(records)}
def handle_http(event):
headers = {k.lower(): v for k, v in (event.get("headers") or {}).items()}
if headers.get("x-api-key") != API_KEY:
return {
"statusCode": 403,
"headers": {"Content-Type": "application/json"},
"body": json.dumps({"error": "Forbidden"})
}
params = event.get("queryStringParameters") or {}
if "par" not in params:
return {
"statusCode": 400,
"headers": {"Content-Type": "application/json"},
"body": json.dumps({"error": "Missing par"})
}
par = int(params["par"])
return {
"statusCode": 200,
"headers": {"Content-Type": "application/json"},
"body": json.dumps({"res": par + 1})
}
What we have in this lambda function:
- SQS messages are parsed as JSON.
- When triggered by API Gateway, the function validates the API key and query parameter.
- The output queue URL and API key are passed via environment variables.
Step 2: Deploy with Terraform
Terraform lets us declaratively set up AWS infrastructure — Lambda, SQS queues, API Gateway, and permissions — in one go.
Project structure:
project/
├── lambda/
│ └── lambda_function.py
└── infra/
└── main.tf
Terraform Configuration (infra/main.tf)
terraform {
required_providers {
aws = {
source = "hashicorp/aws"
version = "~> 5.0"
}
archive = {
source = "hashicorp/archive"
}
}
}
provider "aws" {
region = "us-east-1"
}
locals {
project = "lambda-sqs-api"
}
# Package Lambda
data "archive_file" "lambda_zip" {
type = "zip"
source_dir = "../lambda"
output_path = "lambda.zip"
}
# SQS Queues
resource "aws_sqs_queue" "input" {
name = "${local.project}-input"
}
resource "aws_sqs_queue" "output" {
name = "${local.project}-output"
}
# IAM Role for Lambda
data "aws_iam_policy_document" "assume_role" {
statement {
actions = ["sts:AssumeRole"]
principals {
type = "Service"
identifiers = ["lambda.amazonaws.com"]
}
}
}
resource "aws_iam_role" "lambda_role" {
name = "${local.project}-role"
assume_role_policy = data.aws_iam_policy_document.assume_role.json
}
resource "aws_iam_policy" "lambda_policy" {
name = "${local.project}-policy"
policy = jsonencode({
Version = "2012-10-17"
Statement = [
{
Effect = "Allow"
Action = [
"sqs:SendMessage",
"sqs:ReceiveMessage",
"sqs:DeleteMessage",
"sqs:GetQueueAttributes"
]
Resource = "*"
},
{
Effect = "Allow"
Action = [
"logs:CreateLogGroup",
"logs:CreateLogStream",
"logs:PutLogEvents"
]
Resource = "*"
}
]
})
}
resource "aws_iam_role_policy_attachment" "lambda_policy_attach" {
role = aws_iam_role.lambda_role.name
policy_arn = aws_iam_policy.lambda_policy.arn
}
# Lambda Function
resource "aws_lambda_function" "func" {
filename = data.archive_file.lambda_zip.output_path
function_name = local.project
role = aws_iam_role.lambda_role.arn
handler = "lambda_function.lambda_handler"
runtime = "python3.12"
environment {
variables = {
OUTPUT_QUEUE_URL = aws_sqs_queue.output.id
API_KEY = "testkey"
}
}
}
# Event Source Mapping (SQS → Lambda)
resource "aws_lambda_event_source_mapping" "sqs_trigger" {
event_source_arn = aws_sqs_queue.input.arn
function_name = aws_lambda_function.func.arn
batch_size = 1
enabled = true
}
# API Gateway
resource "aws_api_gateway_rest_api" "api" {
name = "${local.project}-api"
}
resource "aws_api_gateway_resource" "lam" {
rest_api_id = aws_api_gateway_rest_api.api.id
parent_id = aws_api_gateway_rest_api.api.root_resource_id
path_part = "lam"
}
resource "aws_api_gateway_method" "get_lam" {
rest_api_id = aws_api_gateway_rest_api.api.id
resource_id = aws_api_gateway_resource.lam.id
http_method = "GET"
authorization = "NONE"
api_key_required = true
}
resource "aws_api_gateway_integration" "lambda_integration" {
rest_api_id = aws_api_gateway_rest_api.api.id
resource_id = aws_api_gateway_resource.lam.id
http_method = aws_api_gateway_method.get_lam.http_method
integration_http_method = "POST"
type = "AWS_PROXY"
uri = aws_lambda_function.func.invoke_arn
}
resource "aws_lambda_permission" "api_gateway" {
statement_id = "AllowAPIGatewayInvoke"
action = "lambda:InvokeFunction"
function_name = aws_lambda_function.func.function_name
principal = "apigateway.amazonaws.com"
source_arn = "${aws_api_gateway_rest_api.api.execution_arn}/*/*"
}
# API Key and Usage Plan
resource "aws_api_gateway_api_key" "key" {
name = "testkey"
value = "testkey"
enabled = true
}
resource "aws_api_gateway_usage_plan" "plan" {
name = "basic"
api_stages {
api_id = aws_api_gateway_rest_api.api.id
stage = aws_api_gateway_deployment.deploy.stage_name
}
}
resource "aws_api_gateway_usage_plan_key" "plan_key" {
key_id = aws_api_gateway_api_key.key.id
key_type = "API_KEY"
usage_plan_id = aws_api_gateway_usage_plan.plan.id
}
resource "aws_api_gateway_deployment" "deploy" {
depends_on = [aws_api_gateway_integration.lambda_integration]
rest_api_id = aws_api_gateway_rest_api.api.id
stage_name = "v1"
}
output "api_url" {
value = "${aws_api_gateway_deployment.deploy.invoke_url}/lam"
}
Step 3: Deploy and Test
- Initialize Terraform:
cd infra
terraform init
- Apply the configuration:
terraform apply
- Test the API Gateway endpoint:
curl -H "x-api-key: testkey" "<API_URL>?par=10"
# Expected to receive: {"res": 11}
- Test SQS:
Send a message to the input queue:
aws sqs send-message --queue-url <input-queue-url> --message-body '{"par": 5}'
Then check the output queue:
aws sqs receive-message --queue-url <output-queue-url>
# Expected to receive: {"res": 6}
Step 4: Clean Up
To remove all resources:
terraform destroy
Summary
[SQS Input Queue] ─▶ [Lambda Function] ─▶ [SQS Output Queue]
▲
│
[API Gateway /lam?par=N]
│
Secured by API Key
You’ve just built a multi-trigger Lambda that:
- Consumes from and publishes to SQS queues.
- Responds to HTTP requests via API Gateway.
- Enforces an API key using a simple header check.
- Is fully managed through Terraform for reproducible serverless infrastructure.
This pattern is great for lightweight message transformers, hybrid microservices, or bridging asynchronous and synchronous AWS systems — all with a few lines of Python and Terraform.
If you’d like to see a bit more advanced Lambda example using AWS SAM - please check this post: Coding Lambda using AWS SAM + AWS SQS + Python PowerTools
Useful links
- Python Cheatsheet
- Terraform cheatsheet - useful commands and examples
- AWS lambda performance: JavaScript vs Python vs Golang
- Layered Lambdas with AWS SAM and Python
- Coding Lambda using AWS SAM + AWS SQS + Python PowerTools
- AWS CDK Overview, TypeScript and Python Examples and Performance Conciderations

